"A
question came up at home – and that is about use of credit card wallets
that protect from rogue scanners. Are they necessary? Will they be more
or less necessary when newer cards with embedded microchips are more
prevalent?
I thought this might be an interesting topic for your blog."
Thanks for the great question and idea to put this in a blog post!
When it comes to
old-school mag stripe cards… have you noticed how you sometimes have to reinsert or
re-swipe the card in the reader, and even then it doesn’t always read? Mag
stripe is definitely a direct-physical-contact
medium. Other than vendor breaches or stolen (physical) wallets, the typical way
someone can steal your mag-stripe card data is via some kind of
skimmer. There are
very low profile skimmers that can be inserted into
ATMs or
gas pumps to
grab your card data while you’re trying to
do a legit transaction. There are also hand-held or desktop units that
an “evil waiter” can use to grab your card data when they take your
card
at a restaurant. There are no reliable remote ways to read magnetic data
off a card. So, a lead wallet won’t help here
at all. It’s the same way you can’t read the contents of a hard drive
just by being near it.
Next is
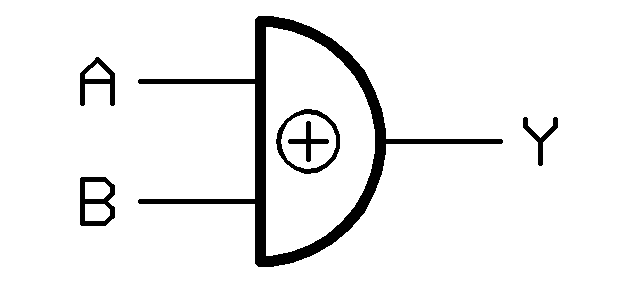
RFIDs. That stands for Radio Frequency IDentification and, as the name implies, they do transmit data. These are the chips in the tap & pay cards.
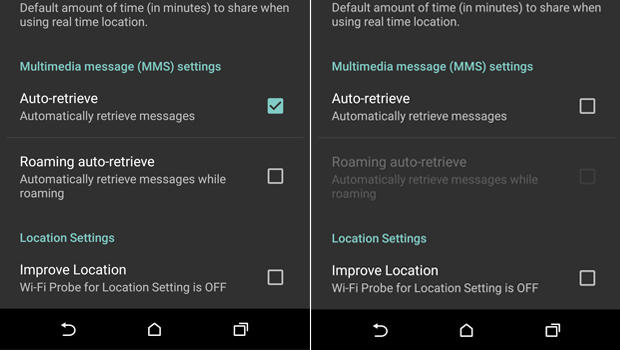
There are transmission-blocking wallets for RFID passports and things like that
which transmit data. So anything with
RFID or a transmitter can be remotely read (at
various distances).

The new cards coming
out will be chip & "something". Currently in Europe they use
chip
&
pin. This is expensive to implement and requires replacing all
the mag stripe readers with much costlier readers.
The chip is a microchip that computes a value and provides a 1-time-use
code for a transaction. Note that it does not use your credit card
number. In addition to that single use code, the person also needs to
put in their numerical PIN. So, even if the
card was stolen, or the code could be remotely read, it couldn’t be
used for a transaction without the PIN, and the code couldn't be reused.
The US is actually
considering
chip & signature. Among the reasons is that the cost will be lower
even though the readers still need to be replaced. (though, because of
the marketing power of Apple and Apple Pay, many
merchants have already upgraded readers). The chip works the same way,
but the 2
nd part of the verification is the physical signature. Not particularly strong but better than nothing.
Now… neither of
these new card types solves a particularly important case…
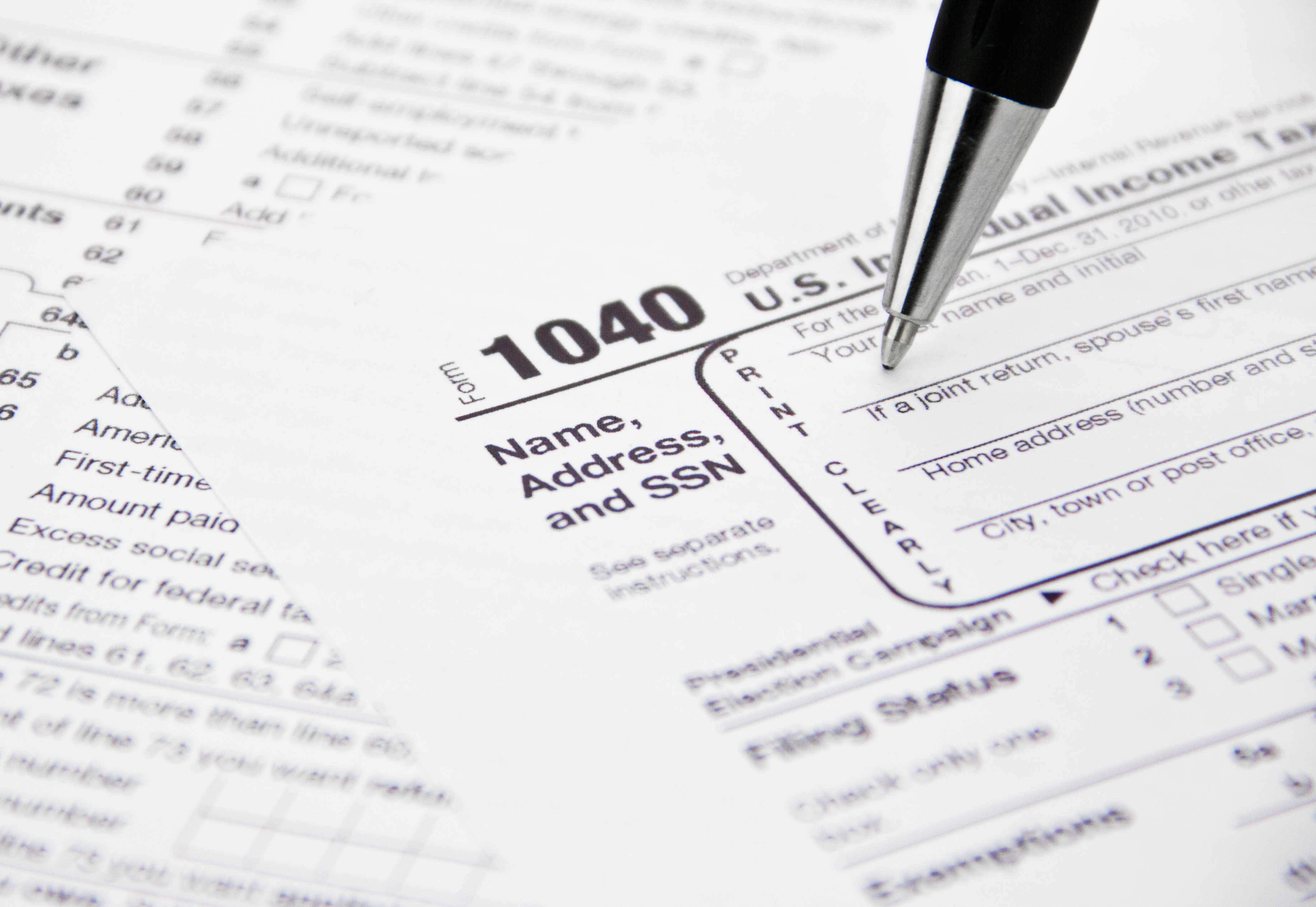
Card Not Present. This is
when you buy something over the phone or internet. So there’s no card
reader nor person to look at your signature, and
you don’t want to give some random merchant your PIN.
There are a
number of potential solutions in the works.
Verified-By-VISA or
MasterCard SecureCode are examples of tools available now, even for mag
stripe cards. Basically, you choose one of these at
online checkout; then you’re transferred to the VISA or MasterCard
site; you authenticate there; the VISA or MasterCard site generates an
acceptance code that get sent back to the merchant and you’re all set.
So, chip &
signature cards and readers will help deal with some of the credit card
fraud we have, but we still need a standardized solution for Card Not
Present (CNP).
Now with that
background, back to your initial question… remote reading of a magnetic
stripe, chip & PIN or chip & signature card is not a major
threat. However, cards that use RFID, or any tap and pay technology,
could be read remotely.
You'd be far better off taking the precautions I listed in my previous ID Fraud articles including:
- regularly viewing your credit report
- watching your bills
- shredding unneeded documents that have personal info
- carrying only the minimum cards you need
- using care online
Thanks again for the great question! If anyone has questions or ideas for things I should write about in the future, please let me know.
 Thanks for the great question! You’ve got some good bases covered:
Thanks for the great question! You’ve got some good bases covered: